The whole point of an authentication service is that it allows the client to prove itself to be trustworthy, or at least to prove itself to be the same nefarious character it claims.
I want to make our existing Active Directory the source for all the following:
- Lists of users allowed to log into the managed infrastructure
- UIDs and GIDs of those users
- Passwords of those users
But I’m striking out on everything except the passwords themselves, and I’ve had that part working for years. So no new progress on that front, despite reading tons of LDAP and NSS howtos, bug reports, etc. So instead, let me lay out our planned implementation and workflow:
- Windows administrator makes a new user account in Active Directory.
- Windows administrator (or sometimes me) logs into the main file server, and runs an nearly-unmodified adduser script that creates the user’s Unix UID, home directory, and registers the user on either our student mailing list or our faculty/staff mailing list. This script currently has a big ‘ssh in a for loop’ part for adding accounts on the client systems, but this will be removed.
- A cron job on the file server runs every two minutes (even-numbered ones) and puts all the usernames, UIDs, and GIDs into a protected file accessible via NFS export. This takes only a fraction of a second to run.
- A cron job on the rest of the Linux systems runs every two minutes (odd-numbered ones — good thing I got time synchronization working earlier, right?), reads the protected file and the contents of our main home directory NFS area, and determines which users should be added and deleted on its local passwd and shadow files. Even on a freshly-reinstalled system with no domain users added, this takes seconds to run.
- Whenever a user gets deleted via our deluser script, the rest of the Linux systems will pick up on the deletion by the fact that their home directory will be owned by root and inaccessible to all other users.
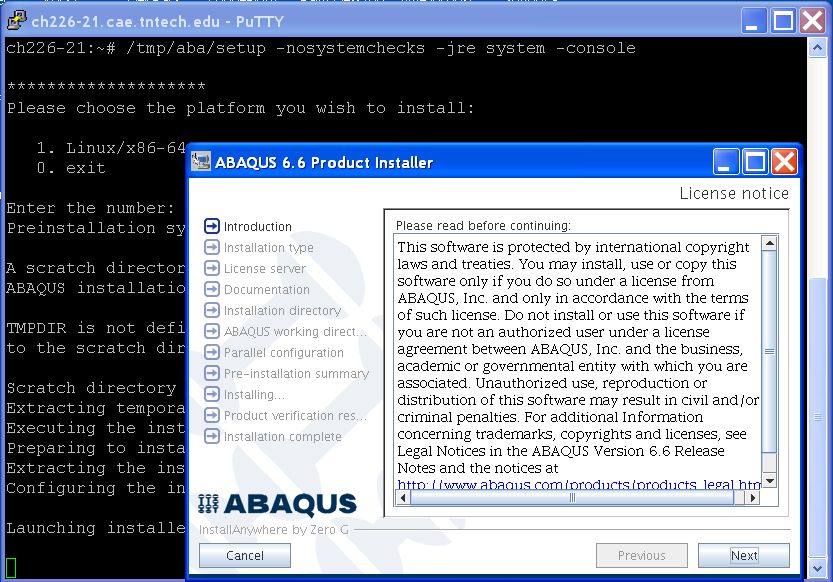
You may have noticed that there’s nothing in any of this about the user’s actual password. It’s only stored on the domain controllers, never on any of the Linux systems. We use Kerberos and PAM to directly authenticate the users against the Active Directory servers. Code and configurations for this setup after the jump. Continue reading “Authentication Servers”